You are viewing the RapidMiner Deployment documentation for version 9.7 - Check here for latest version
Users, Groups and Roles
This page will guide you through the most common tasks of user, group and role management. The scenarios described on this page apply for the default identity and security configurations shipped with our RapidMiner Platform deployment templates. See below for the defaults we chose and how to manage them.
For a quick recap on concepts and terminology, read our security overview.
Pre-requisites
To carry out the management tasks described below, you need to be logged in with a user that has the appropriate role assigned. In our default configuration, this role is covered by the platform-admin realm role, which is assigned to the pre-provisioned admin user.
After logging in, navigate to Identity and Security on your deployment's landing page to access the admin interface. All instructions below assume that you are already logged in and navigated to this page.
Managing users
By default, only a single admin user is created in a RapidMiner platform deployment. This user has admin privileges across all platform components. We strongly encourage provisioning users for each person that will interact with the RapidMiner Platform, either as a user or an admin. This is a good practice that also enables clear audit trails.
User database and identity provider federation is also supported, which removes the administrative burden of managing users and is tipically a requirement in enterprise environments.
If you are upgrading from a previous version of the RapidMiner Platform, or from a standalone RapidMiner Server installation, please consult our Upgrade and Migration Guide to provision your previously existing users.
Adding users
Adding users is a two-step process: first you have to create the user, then you have to assign (temporary) credentials so the user can log in.
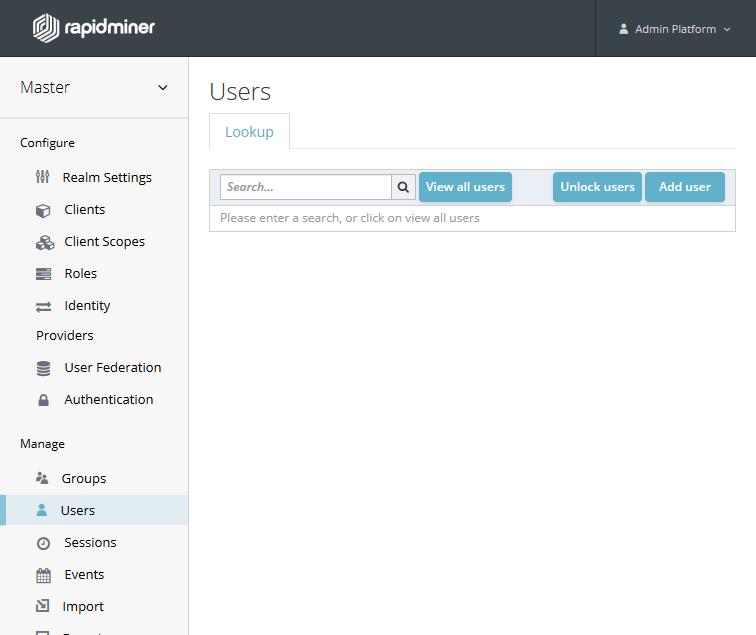
Go to the Users menu and click on Add User.
The only mandatory field you need to provide is the username (we will provide the initial password in the next step). Here's a short list of the other settings you can choose:
- If you are filling out the user's e-mail address and you know it to be valid then go ahead and set Email verified to On.
- If you want the user to fill in their profile information (name and email) then add Update Profile to the list of Required User Actions. This will display a form for the user when logging in for the first time to provide their data.
- If you want the user to change their password on the next login, add Update Password to the list of Required User Actions.
- If you want the user to configure two-factor authentication on the next login, add Configure OTP to the list of Required User Actions.
When you click Save, the user is created and the user details page is shown.
The second step is to set a (temporary) password for the user. To do this, go to the Credentials tab and add the user's new password to the Password and Password confirmation fields. By default, the password you set will be a temporary one and the user will have to change it on their first login. To change this, set Temporary to Off.
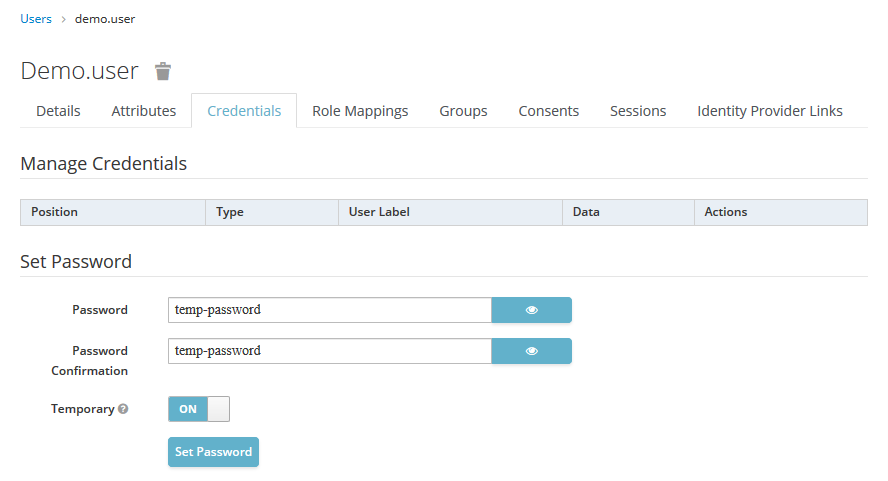
When you click Save, the user's initial password is stored, and they now should be able to log in.
By default, users are assigned the platform-users role, which gives them access to all components of the RapidMiner Platform as regular, non-privileged users. See the chapter on roles if you wish to change this default.
Removing users
Go to Users, and find the user to be deleted. You can either use the search box, or click on View all users and find them on the displayed list.
Click on Delete in the user's row and confirm the action.
Resetting a user's password
It's a typical administration task to trigger a password reset for a user, in case they forgot their credentials (and this is not possible in a self-service fashion because emails and password resets are not configured).
Go to Users, and find the user who needs a password reset. You can either use the search box, or click on View all users and find them on the displayed list. Click on Edit.
On the Credentials tab, in the Reset Password section, add the user's new password to the Password and Password confirmation fields. By default, the password you set will be a temporary one and the user will have to change it on their next login. To change this, set Temporary to Off.
Impersonating users
Impersonation can be a very useful tool when you are trying to identify an authentication or authorization problem for a specific user. It allows you to see the "world" of the RapidMiner Platform with that user's eyes, without needing to ask for their password, or scheduling a timeslot with the user.
Go to Users, and find the user to be deleted. You can either use the search box, or click on View all users and find them on the displayed list.
Click on Impersonate in the user's row.
You need to log out and log back in with your own user to stop impersonating.
Managing groups
Groups manage groups of users. You can map roles to a group. Users that become members of a group inherit the role mappings that group defines.
Groups can be nested to an arbitrary level, if such level of granularity is desired.
By default, no groups are provisioned.
Adding groups
Go to Groups, and click on New. Provide the group name and click Save.
To assign a role to this group, click on the Role Mappings tab and add the desired roles. To add realm roles, select them from the list of Available Roles and click Add Selected >. To add client specific roles (e.g. you only want to allow the group to access Dashboards), first find that client in the Client Roles dropdown (you need to start typing its name), and then adding the desired roles by selecting them and clicking on Add Selected >>.
To add a sub-group that is nested in an existing group, the process is very similar. Go to Groups, then make sure to select the parent group before clicking on New. Follow the instructions above to complete your task.
Removing groups
Go to Groups, select the group or sub-group you wish to delete, then click on Delete. Confirm your action to complete the task.
Note: deleting a group will also delete its nested sub-groups without any additional warnings.
Changing default groups
You can choose which group newly created users are added to automatically.
Go to Groups, then click on the Default Groups tab. Find the group in the list of Available Groups (either by using the search box or the View all groups button) and click on it to select it. Finally, click Add to complete the task.
Adding and removing users to groups
Go to Users, and find the user you wish to add. You can either use the search box, or click on View all users and find them on the displayed list. Click on Edit in the user's row.
To add the user to a group, click on the Groups tab. Find the group in the list of Available Groups (either by using the search box or the View all groups button) and click on it to select it. Finally, click Join to complete the task.
To remove the user from a group, click on the Groups tab. Find the group in the list of Group Membership (either by using the search box or the View all groups button) and click on it to select it. Finally, click Leave to complete the task.
Managing roles
Roles describe what components users have access to in the RapidMiner Platform, and what specific actions they can do in these components. Various components (called clients in KeyCloak terminology) can have their own set of roles, and the entire deployment also defines a set of roles, called realm roles. To simplify role definition and management, the concept of composite roles exists, which allows a realm role to "bundle" a set of realm and client roles together.
By default, we provision three composite realm roles: platform-users, platform-admin and platform-webservice-access.
platform-usersrole authorizes users to access all RapidMiner Platform components as regular, non-privileged users.platform-adminrole authorizes users as administrators for each component, and it provides privileges to access the Identity and Security component.platform-webservice-accessis a restricted role which should only be used for secure web service access.
The table below summarizes the various client roles and their relationship to these realm roles.
| Component | Role | platform-admin | platform-users |
|---|---|---|---|
| Dashboards | admin | |
|
| editor | |
|
|
| viewer | |
|
|
| JupyterHub | administrator | |
|
| user | |
|
|
| Landing Page | view-landing-page | |
|
| Platform Admin | python-env-admin | |
|
| python-env-viewer | |
|
|
| rts-admin | |
|
|
| rts-deployment-admin | |
|
|
| rts-viewer | |
|
|
| RapidMiner Server | administrator | |
|
| analyst | |
|
|
| connection manager | |
|
|
| execute | |
|
|
| report editor | |
|
|
| report manager | |
|
|
| report viewer | |
|
|
| scheduler | |
|
|
| service | |
|
|
| users | |
|
|
| Token Generator | users | |
|
Adding roles
If your organization needs roles to be more restrictive on which users get access to what components of the RapidMiner Platform, you can define your own.
You should use composite realm roles for this purpose. The components of the RapidMiner Platform operate with a predefined set of client roles and changing them may cause problems. The one exception to this rule is RapidMiner Server. See the chapter below on how to configure roles and RapidMiner Server groups.
To add a new role, go to Roles and click on Add Role. Enter the new role's name and click Save.
On the Details tab, set Composite Roles to On. The Composite Roles section will appear below.
To add realm roles, select them from the list of Available Roles and click Add Selected >. To add client specific roles (e.g. you only want to allow the group to access Dashboards), first find that client in the Client Roles dropdown (you need to start typing its name), and then adding the desired roles by selecting them and clicking on Add Selected >>.
Assigning roles to users
Go to Users, and find the user you wish to assign a role to. You can either use the search box, or click on View all users and find them on the displayed list.
Click on Edit in the user's row, then click on the Role Mappings tab. You will see all the realm roles and client roles that the user is assigned to (to see client roles for a specific client, you need to select it from the Client Roles dropdown by typing the client's name).
To add realm roles, select them from the list of Available Roles and click Add Selected >. To add client specific roles, first find that client in the Client Roles dropdown (you need to start typing its name), and then adding the desired roles by selecting them and clicking on Add Selected >>.
You can use the same interface to remove assigned roles.
Changing the default roles for new users
Newly created users get the platform-users role by default.
To change this, go to Roles and click on the Default Roles tab.
To add realm roles, select them from the list of Available Roles and click Add Selected >. To add client specific roles, first find that client in the Client Roles dropdown (you need to start typing its name), and then adding the desired roles by selecting them and clicking on Add Selected >>.
Roles and their relationship to RapidMiner Server
There's a mismatch in terminology between the RapidMiner Platform's Identity and Security component and RapidMiner Server, when it comes to groups. Roles in the Platform correspond to Groups in RapidMiner Server.
One typical use-case for creating a new group is restricting execution queues to members of certain RapidMiner Server Groups. To make sure that this correctly maps to users and roles defined in RapidMiner Identity and Security, please follow the steps below.
First, log in with a user who has the platform-admin role and go to Identity and Security.
Go to Clients, find urn:rapidminer:server and click on Edit in its row.
On the Roles tab, click on Add Role and provide a name for your new role. Click Save.
Next, go to RapidMiner Server, and click on User Management under Administration. Click on Add groups. Use the same name for your group as you used for the client role and click Submit.
On the Groups tab, click on your newly created group's name to open the group details page. On the following screen, click on the Manage LDAP/SAML/Keycloak groups action. Enter the name of the new group and click Add.
Go back to the group details page, and check Group managed by LDAP/SAML/Keycloak (If selected, members of the LDAP/SAML/Keycloak groups specified below are automatically added to this group upon login). The panel below will change to one that lists groups.
On this panel, select the newly created group and click Copy. Click Submit to save your changes.
Now your RapidMiner Server group is ready to use and configured correctly as a client role in Identity and Security.